Kaa IoT Platform Features for Enterprise IoT Projects
Architecture overview
Kaa is an end-to-end IoT platform applicable for any scale of enterprise IoT projects. It provides a range of features that enable developers to build advanced applications for smart products, flexibly manage their connected devices via the cloud, orchestrate end-to-end data processing, analyze device telemetry, and many more. With the IoT features provided out of the box by Kaa, you can create your IoT applications up to 10 times faster than before.
All the features in Kaa are implemented with portable microservices, and Kaa, as a whole, is based on a flexible microservice architecture. This means that you can separately customize each Kaa feature, add new ones, or replace any existing ones with some third-party tools.
Out of the box, Kaa provides all the IoT features you may need for a typical IoT application - from data collection and device management to IoT dashboards and analytics. You can also take advantage of open APIs to integrate Kaa features to your own modules and applications.
The following diagram illustrates the general functional architecture of Kaa.

Connectivity
The connectivity feature is all about messaging between the cloud and connected devices. By using connectivity protocols and related security features, IoT devices access the cloud to send or receive data, and perform different remote actions.
The Kaa platform supports popular lightweight IoT protocols for device connection, such as MQTT and HTTP. At the same time, Kaa is transport-agnostic and may support any IoT protocol that you create and add to the platform. Also, the platform allows building applications that function over any type of network connection, either persistent or intermittent.
The choice between MQTT and HTTP transport depends on your device communication needs. MQTT is fully open, asynchronous, and allows for arbitrary message formats. Unlike MQTT, HTTP binding is synchronous: it follows the request-response communication pattern and does not support server message push. Furthermore, you can choose between encrypted and unencrypted channels for both MQTT and HTTP. Use the encrypted channel for sensitive data or the unencrypted channel for open data.
In case your device does not have an IP connectivity or already implements some communication capabilities, Kaa employs a gateway architecture where a gateway talks to the device over a local network protocol or a proximity protocol, and performs transport-level message conversion or even represents them to the cloud.


Device management
To enable the device management feature, Kaa provides a register of digital twins, which represent things, devices, and other entities managed by the platform. Kaa also allows you to store device attributes, which provide more detailed information about any characteristic of the device. Examples of such attributes could be a serial number, MAC address, location, software version, etc. In addition to simple data types, attributes can contain more complex, structured objects, such as a list of connected peripherals and their properties.
Furthermore, you can construct filters based on the device attributes to segment your device population into individually managed groups. In Kaa, filters get automatically re-evaluated whenever the device attributes change.
To connect to the platform, a device has to present valid credentials, such as pre-shared keys, tokens, login and password combinations, certificates, etc. You can use Kaa credential management APIs to provision, suspend, or revoke access.
Kaa tracks the device throughout its lifecycle, from the initial provisioning and connectivity events to software updates and final decommissioning. You can create and assign custom handlers to automate the corresponding workflows.
Data collection
Out of the box, Kaa provides an easy to use protocol for collecting data from connected devices. This protocol ensures reliable data delivery with response codes, which indicate the result of data processing by the platform. Once received by the platform, the device data can be dispatched to multiple processing pipelines. In case there is any error in the middle of processing, disk crash, or processor overload, the device is notified of that. As a result, the device always knows whether the submitted data is safe to delete or should be resent.
To minimize network usage and improve the data throughput, the protocol supports batching. It provides your devices with the capability to buffer data locally before uploading it in one message. Additionally, intermediary gateways can perform the store and forward function. Besides optimizing the network efficiency, this capability is useful in IoT deployments with intermittent connectivity and helps preserve the device battery life.
Kaa allows you to collect both structured and unstructured data. It can be of primitive types, such as plain numbers or text, or compound, such as key-value maps, arrays, or nested objects.


Data processing and analytics
Kaa gives you a lot of freedom in processing of collected data. The platform features data collection adapters that allow sending data to various databases or data analytics systems. Owing to a highly modular architecture of Kaa, a new integration requires minimum effort to modify an existing adapter or create your own.
Raw, unstructured data can also be transformed into well-structured time series, convenient for analytics, pattern analysis, visualization, charting, etc. Similarly to raw data, time series can be pushed into a processing or analytics system of your choice. Out of the box, Kaa is seamlessly integrated with Open Distro for Elasticsearch, which provides advanced analytics, visualization, and alerting features for Kaa users.
Working with time series is very flexible with Kaa. Apart from displaying the main value for a time series, e.g., temperature, the platform allows users to set up tags, which allow viewing some additional data, such as location, light intensity, humidity, etc. Tag values are extracted from the collected raw data and attached to each data point in a time series. Also, it is possible to build multiple time series from one data sample.
Time series consumers can listen to new data points and trigger particular actions, for example, send mobile push notifications.
Data visualization
The data visualization feature of Kaa comprises a rich set of widgets, such as gauges, charts, maps, tables, etc. You can use these widgets to visualize different types of data, whether telemetry, statistics, geolocation, metadata, filters, software updates, or other—both historical and current. All widgets are configurable and allow you to change their data sources as well as visual representation. To address special use cases, Kaa visualization component allows you to easily plug in custom widgets.
Besides data visualization, widgets allow you to interact with devices by sending commands, changing configuration and metadata, etc.
Dashboards help you organize widgets into logical groups and define their layout. Dashboards can be hyperlinked to streamline navigation in the complex multi-device data sets. Moreover, Kaa supports dashboard templating, which allows you to reuse one configuration for multiple device dashboards.
Owing to its open APIs for third-party system integration, Kaa can be connected to data visualization and exploration tools of your own choice.


Alerts, triggers, and notifications
Kaa is pre-integrated out of the box with the Open Distro for Elasticsearch, a powerful open-source analytics platform. After you add a device to the Kaa platform, you can synchronize live and historical time series data with the Open Distro via its Kibana visual interface. You can then query the device time series by specific parameters and telemetry types, restrict the value ranges in the chart, and get as detailed information on your device activity as you need. It also allows you to customize your data charts, filter and query data, and quickly set up alerts based on your analytics.
For smart alerts and notifications you can easily configure and use various communication channels, such as email, Slack, SMS, push notifications, etc. It is also possible to set up specific actions based on preconfigured data thresholds, thus enabling basic rule engine functionality for your IoT projects. Despite its advanced features, the user interface of Kibana is quite easy to learn and also allows for flexible configuration.
In case of multiple tenants, each tenant’s data is completely isolated and the Kaa-based security access policies are seamlessly carried over to Open Distro and Kibana environments.
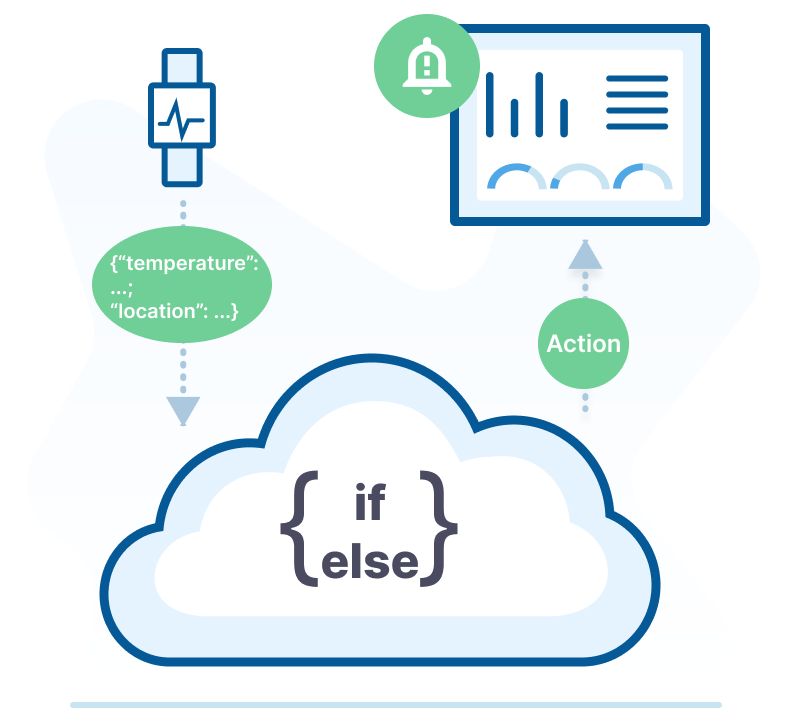
IoT Rule Engine
The Kaa IoT Rule Engine enables you to create complex rules that trigger actions based on data from your IoT devices. You can use the Rule Engine to create alerts, notifications, and other automated responses to events in real time. The Rule Engine also supports aggregation operations, which allow it to process multiple documents and return computed results.
A rule is defined by a JavaScript expression. It remains dormant until coupled with at least one trigger and one action. Your IoT ecosystem can automatically make quick, well-informed decisions thanks to the combination of these three components.
The Kaa IoT Rule Engine is a powerful tool that can be used to create automated responses to events from your IoT devices. It is flexible, scalable, reliable, and easy to use.

Configuration management
Configuration management is essential for controlling the device behavior, managing data processing parameters, edge analytics, feature flagging, and other functions. The Kaa platform allows you to implement all of this functionality by providing the configuration management feature that works with arbitrary data structures. Thus, you can apply the configuration data that is as simple as a set of key-values or as complex as nested objects. Since IoT devices might not be constantly connected, Kaa tracks already applied configuration data as well as pending delivery.
The default configuration management protocol of Kaa supports both the push and pull modes. In other words, a device may subscribe to be notified whenever the configuration is changed on the Kaa server or, alternatively, may periodically poll for changes itself. To ensure reliability, the configuration delivery is based on configuration application confirmations and result codes.
When the device changes its current configuration, Kaa generates a configuration change event. These events may be used to trigger different actions and automation processes inside and outside the platform.
The Kaa platform allows you to manage configuration of the devices individually or at scale. You can define configuration for a specific device or for a group of devices based on their individual characteristics, such as software version, location, or other attributes.
Command execution
Command execution is one the key Kaa features for IoT development that allows you to deliver messages with the arbitrary payload to connected devices, execute commands, and receive near-real time responses. For example, you can remotely check current temperature on a home thermostat, point a security camera to a specific area, open a vehicle trunk, and so on.
Kaa implements the two-way communication that allows devices to send a response back to the server. The caller can wait for the response either synchronously or asynchronously. For lightweight commands you may go with the synchronous option meaning that the caller will be put on hold until the command execution result is delivered. For the resource-consuming commands you may choose the asynchronous option, which enables the platform to notify the caller about the command execution result.
From the device perspective, the Kaa platform supports both push and pull models of delivery: a device can either periodically check for new commands or rely on the server to push them. In the case of constrained devices that are unable to maintain a persistent session, Kaa can buffer scheduled messages until they are successfully delivered or timed out.


Over the air updates
OTA updates enable your devices to evolve over time. You can implement and distribute new IoT features for the devices that are already in use, for example, face recognition for security cameras, autonomous driving for vehicles, predictive maintenance for industrial machinery, etc.
Kaa allows you to reliably deliver software updates by utilizing the confirmation response codes sent by devices upon the update result. Another valuable feature is the ability to define the software update path by using the compatibility graphs based on semantic versioning. Buggy versions can be easily rolled back.
Out of the box, Kaa allows tracking the current software version installed on the managed devices as well as defining potential update vectors. Each software version is represented in Kaa by a flexible descriptor that is delivered to the device as an instruction to perform an update. For example, common descriptor fields include the download URL, the new software version name, the file size, checksums, etc. With this information, the device can easily download the new software, validate its integrity using checksums, install, and report back success.
Multitenancy
The Kaa platform supports advanced multitenancy, which means that a single Kaa instance may serve multiple independent tenants and each tenant’s data is completely isolated from other tenants. In this case, each tenant has a fully isolated share of the Kaa instance where they manage their own users, user permissions, applications, devices, dashboards, etc. The tenants can be thought of as separate organizations that access your Kaa-based solution.
Technically speaking, the Kaa platform tenants are implemented on top of Keycloak realms so that each tenant has a separate Keycloak realm. That’s why you may not only work with tenants and their credentials but also use the Keycloak functionality on a very granular level to manage realms, scopes, resources, roles, identity providers, etc.
For greater flexibility and independence from any specific Keycloak version, Kaa allows using templates for tenants creation. Templates enable solution admins to create and reuse tenant specifications at different stages of the solution lifecycle, which speeds up tenant setup and customization.


Kaa Identity and Access Management (IAM)
Kaa Identity and Access Management (IAM) provides you with simplified and secure control over your operating security. The data your company accumulates needs to be protected from bad-faith actors and from unauthorized access, you need a single, easy-to-use solution, provided by a team of experts you can trust to protect your interests. Manage user data easily with our solution, focus on your fundamentals, and save costs of developing your own in-house IAM system.
We offer up to 70% reduced spending for use policies and customer management setup costs, thanks to built-in user profile access templates and policies. You can assign access policy in minutes, configure group membership, and implement new security policy enforcement via our intuitive UI. It's an ideal solution for combining multiple user profile mapping across various apps or services, and securely passing user attributes to assign internal or external resources management.
Our IAM tool stands out against other alternatives thanks to its flexibility, allowing access to multiple clients and additional development possibilities while remaining a stable anchorage for your businesses’ security. We provide centralized access for millions of resources that’s easy to use and adaptable to your company’s specific needs. The IAM tool we can offer to you has been tried and tested by dozens of companies working in multiple industries and can transform your corporate safety.
