IoT Security and Privacy: Challenges with Solutions
April 10, 2024Today's world is globally connected with Internet of Things (IoT) technology, providing an extensive convenience level, but simultaneously, they are raising exact issues of privacy and security. With an increasing number of different IoT devices spreading fast across various spheres of smart households and industrial systems, the issue of appropriate data protection as well as secure communication channels is becoming core.
This article covers IoT security and privacy concerns, delving into its significance, the inherent risks and challenges IoT devices face, and some examples of security breaches.
IoT security meaning and its importance
IoT security system means protecting connected devices and networks within the IoT ecosystem from potential risks and security breaches. This entails safeguarding products such as SCADA systems, smart homes, and surveillance cameras from unauthorized access or malicious attacks. It involves identifying, monitoring, and mitigating risks to guarantee the availability, integrity, and confidentiality of IoT items, apps, data, and network links.
Mobile devices like smartphones and IoT devices mostly lack built-in security protection. They may come with vulnerabilities that hackers can use. They have particular security problems as they send data to the cloud usually. Extensive IoT security system strategies must include component hardening, continuous monitoring, firmware updates, access management in iot, threat response, and vulnerability management.
Security and privacy in IoT are significant due to the vulnerable nature of IoT devices and the increased use of IoT hardware. They usually are not equipped with an encryption key, making them vulnerable to attackers who can penetrate the whole network if a single device gets compromised. In contrast with traditional devices which do not have strong security features by design and are non-updatable after the manufacturing process, IoT devices rely on different security solutions at various phases of their lifecycle. The IoT systems, which are highly interconnected, imply that the network is as strong as its weakest link, allowing the hackers to move across the device to the device after getting their foot into it.
In addition, the IoTs used in corporate networks can open a backdoor for attackers to invade and harm confidential data.
Different security techniques advance IoT device protection through device profiling, zero-trust architecture, and limiting the number of network endpoints. Besides, standards and frameworks such as the IoT Security Foundation (IoTSF) and the National Institute of Standards and Technology (NIST) provide security architecture guiding IoT systems development.
IoT security and privacy issues
IoT systems face various security issues and challenges that need to be addressed to ensure the integrity and confidentiality of data protection of critical infrastructure. Some key security challenges in IoT systems include:
Insufficient industry-leading
IoT devices have become attractive for spheres of industry like automobiles and healthcare as they help to improve effectiveness and reduce expenditures. Unlike humans, who can make errors or become distracted. IoT devices are at risk of cyber attacks since they are innately connected to the internet. The companies are prone to exposing themselves to cyber risks because they have sometimes failed to invest in the cybersecurity aspects of their devices.
Lack of skills
Skills shortage also impacts many sectors like IoT, which presents additional challenges. The confluence of IT and OT experts is fundamental to the success but is limited in practice. On the other hand, IoT is also an important field apart from being an interdisciplinary field like cybersecurity, UX design, AI, and app development. The role of educating consumers about the security issues surrounding IoT, and more particularly, smart home devices is crucially important.
Shadow IoT
IT professionals are grappling with a growing challenge known as shadow IoT, where IoT devices operate outside the network without oversight, posing security risks. Customized IP-addressed products, such as fitness trackers and digital assistants, enhance convenience but often overlook security. Without visibility into these devices, administrators can’t ensure they meet security standards, or detect malicious activity, leaving openings for system breaches and cyber-attacks like privilege escalation or botnet infiltration.
Privacy attacks
Many IoT devices come with default administrator usernames and passwords, often insecure ones like "password." Compounding the issue, all devices of the same model may share these credentials. In some cases, resetting these credentials isn’t possible. Attackers exploit this vulnerability, often successfully, as they're aware of these defaults. For example, the Mirai attacks of 2016 targeted IoT devices with factory-default or hard-coded passwords, allowing fraudsters access to servers.
DNS vulnerabilities
Many companies leverage the IoT to gather data from older equipment, which may lack modern security standards. Integrating legacy devices with IoT can expose networks to vulnerabilities associated with outdated equipment. IoT device connections often rely on DNS, a decentralized system from the 1980s that may struggle to support installations of numerous units. Hackers exploit DNS weaknesses in DDoS attacks and DNS tunneling to steal data or deploy malware.
Resource shortage
The restricted capabilities of numerous IoT devices present a security concern. Many lack the processing power for robust security measures like firewalls or antivirus software. Some devices even struggle to connect with others, leaving them vulnerable to attacks. For instance, recent data breaches have targeted Bluetooth-enabled IoT devices. In the automotive sector, cybersecurity experts revealed vulnerabilities in Bluetooth tech that could be exploited to hack vehicles. Similarly, vehicles using wireless FOB keys have been targeted, with attackers cloning these keys to steal vehicles undetected.
Examples of IoT security breaches
Mirai Botnet (aka Dyn Attack)
In October 2016, the Mirai botnet targeted the internet using a botnet of IoT devices, crippling Dyn servers and bringing down huge sections of the internet, affecting media titans like Twitter, Reddit, CNN, and Netflix.
TRENDnet webcam hack
TRENDnet's SecurView cameras were hacked, allowing anyone to access the cameras' IP addresses and record audio and video. This happened due to faulty or malicious software that let anyone access the webcam.
Verkada hack
Verkada, a cloud-based video monitoring and recording service, was hacked in March 2021, giving attackers access to private information belonging to Verkada software clients and over 150,000 hospitals, schools, prisons, and other sites using legitimate admin account credentials found on the internet.
Stuxnet attack
In 2010, a uranium purifying plant in Natanz, Iran, was attacked by hackers who planted malware in the Siemens Step7 software running on Windows. This allowed them to control different machines at the industrial level with just one command and access confidential blueprints and sensitive information about the industry.
Jeep hack
In July 2015, researchers took control of a Jeep SUV via the Sprint cellular network by exploiting a firmware update mechanism. They could control the vehicle's speed and even steer it off the road.
Target's сredit сard breach
In 2013, hackers stole credit and debit card information from 40 million customers by exploiting a vulnerability in Target's security and payment system.
These examples highlight the importance of robust IoT security measures to protect sensitive data and prevent unauthorized access to critical infrastructure.
4 Main security and privacy issues in IoT
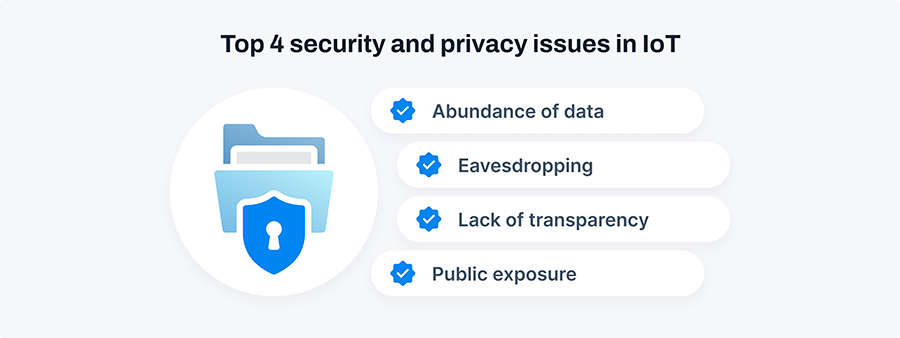
Privacy concerns in IoT are significant due to the vast amount of data generated by IoT devices and the potential for breaches and misuse.
Addressing IoT privacy concerns requires a multi-faceted approach involving consumer awareness, regulatory frameworks, industry standards, and secure-by-design principles. Educating consumers about the risks associated with IoT devices, enhancing transparency in data collection practices, and implementing regulations that prioritize user privacy are essential steps toward mitigating privacy risks in the IoT ecosystem.
1. Abundance of data
The sheer volume of data produced by IoT devices creates numerous entry points for hackers, leaving sensitive information and devices vulnerable to breaches.
2. Eavesdropping
Hackers can exploit unencrypted data from IoT devices to eavesdrop on users, invading their privacy by monitoring activities like watching TV shows or other personal information.
3. Lack of transparency
Many IoT devices lack clear interfaces or mechanisms to provide users with information about data collection and usage, making it challenging for individuals to understand how their personal information is being handled.
4. Public exposure
IoT devices frequently gather personal data, which manufacturers or businesses may use for various purposes such as employment assessments or determining insurance rates, potentially subjecting individuals to unwelcome public scrutiny.
How can IoT security?
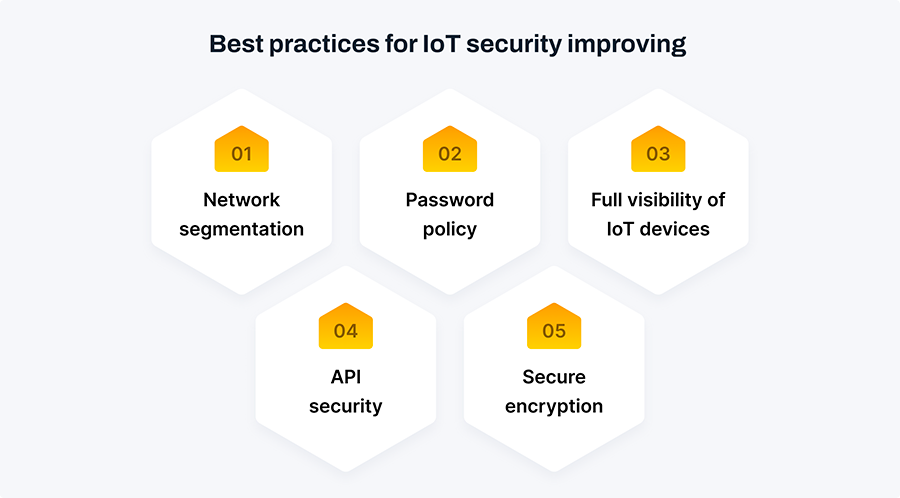
Until recent years, IoT security wasn't a top priority, but a series of damaging hacking incidents changed that. Now, there's a push for IoT security solutions to fix vulnerabilities and stop breaches before they happen. Ensuring robust security measures is primary to safeguarding sensitive data, protecting critical infrastructure, and mitigating cyber threats.
Network segmentation
Network segmentation aims to reduce the risk of cyber attacks by dividing a network into smaller, separate subnetworks. This separation provides more control over traffic flow between devices, making it harder to spread across the network. By isolating IoT devices in their network segments and limiting their access to other parts of the network, organizations can enhance security. Using technologies like virtual LAN setups and next-generation firewalls, businesses can create these segmented networks to protect against lateral attacks. Regular monitoring of network segments helps detect any unusual activity and allows prompt action to address potential threats.
Password policy
Weak password security policies remain a leading cause of IoT device breaches. To protect your devices, it's crucial to maintain strong password practices. Many IoT devices come with default passwords that are easily accessible online and lack sufficient strength. Upon initial connection to your network, it's advisable to change the default password to a stronger, unique one for each device. Regularly updating passwords is essential, and enforcing periodic password changes can enhance security. Utilizing a password vault can also help prevent unauthorized access and safeguard sensitive data.
API security
API security is crucial for protecting data transmitted between IoT devices and backend systems. Hackers can exploit vulnerabilities in these channels, underscoring the need for robust API security measures. The T-Mobile data breach in 2018, caused by a compromised API, exposed sensitive customer information, highlighting the risks of inadequate API security.
Secure encryption
When setting up IoT devices, encrypted communications are crucial. Without encryption, hackers can easily analyze plain-text protocols for vulnerabilities. To secure online traffic, always use HTTPS, TLS, SFTP, and DNS security extensions. IoT devices connecting to mobile apps should also use encrypted protocols, and data stored on flash drives must be protected. Encryption ensures data security and guards against malware. PKI, with its two-key cryptosystem, simplifies encryption and decryption, enhancing overall security for private transactions online.
Full visibility of IoT devices
The organization should commence interaction by realizing several IoT-connected devices to their network now. Enumerating different devices deployed and keeping track of all IoT assets is an essential task for successful data security. This inventory needs to cover the manufacturer's information, device Model ID, serial number, hardware and software versions, embedded firmware, operating system, and configuration set for each device.
Knowing the risk profile of the respective device and how it communicates with other network devices is one of the main things. Such data can be used for fine-grained network segmenting, and subsequent firewall policy creation aimed towards better security.
Conclusion
Therefore, the growing IoT causes the necessity of the tri-lateral approach for perfect security and privacy. With the intersection network of interconnected devices in our lives, the ethical danger of data leaks and privacy infringements becomes a matter of concern. Addressing the convergence of vulnerabilities across various sources within IoT infrastructure is paramount. We must work to resolve these issues to ensure the security and integrity of the entire system. Data protection through security protocols, transparency, and authority given to users can take us through the journey of this universal wired environment. As we achieve synergy and attentiveness we can make great strides in ensuring that our private information and digital security are protected in the fast-paced world that we live in.
FAQ
How can IoT be used for security?
IoT can enhance security through smart surveillance cameras, motion sensors, and access control systems, enabling real-time monitoring, automated alerts, and remote access control, bolstering overall security measures.
How do I ensure privacy in IoT?
Ensure privacy in IoT by using strong encryption, limiting data collection to essential information, providing consent mechanisms, regularly updating device software, and implementing robust access controls.
What are the three types of IoT security?
The three types of IoT security are device security (protecting individual devices), network security (safeguarding data transmission), and cloud security (securing data storage and processing).
How does IoT affect our privacy?
IoT collects vast amounts of personal data, raising concerns about unauthorized access, breaches, and surveillance. Unauthorized data usage and inadequate security measures can compromise individuals' privacy.
Why is IoT security so important today?
IoT security is crucial today because IoT devices collect sensitive data and connect to networks, making them vulnerable to cyberattacks. Breaches can lead to data theft, privacy violations, and disruption of critical systems.
What is IoT security architecture?
IoT security architecture comprises layers of protection, including device, network, and application security, alongside encryption, authentication, and access controls, ensuring comprehensive defense against cyber threats.
What is the weakest point of IoT security?
The weakest point of IoT security often lies in device vulnerabilities, including inadequate authentication, outdated software, and poor encryption, making them susceptible to exploitation by cyber attackers.